
A computer, working or home, is very vulnerable for all sorts of intrusions from the outside. It can be both Internet attacks and actions of foreign users who have received physical access to your car. The latter can not only inexperience damage important data, but also to act malice, trying to identify some information. In this article we will talk about how to protect the files and system settings from such people using a computer lock.
Block your computer
The protection methods that we will talk below are one of the components of information security. If you use a computer as a working tool and store personal data and documents that are not intended for other people's eyes, then it is necessary to take care that with your absence no one can access them. You can do it by blocking the desktop, or logging into the system, or the entire computer. Tools for implementing these schemes There are several:- Special programs.
- Built-in function.
- Block using USB keys.
Then we will describe in detail each of these options.
Method 1: Specialized Software
Such programs can be divided into two groups - system access limits or desktop and blocks of individual components or disks. The first one relates a fairly simple and convenient tool titled Screenblur from the developers of Indeep Software. The software works correctly on all versions of Windows, including the "dozen", which cannot be said about its competitors, and at the same time is completely free.
Download screenblur
Screenblur does not require installation and after launch is placed in the system tray, from where you can access it to the settings and perform the lock.
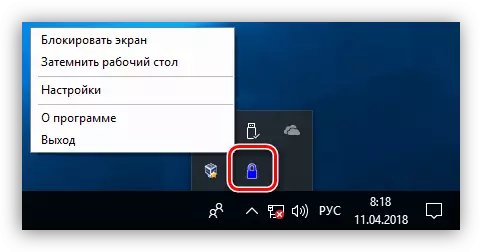
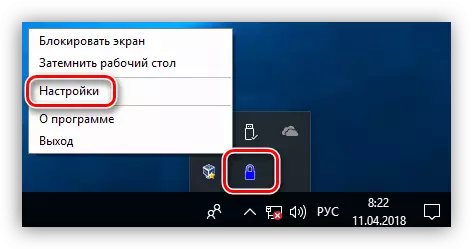
- To configure the program, press the PCM on the TREE icon and go to the appropriate item.
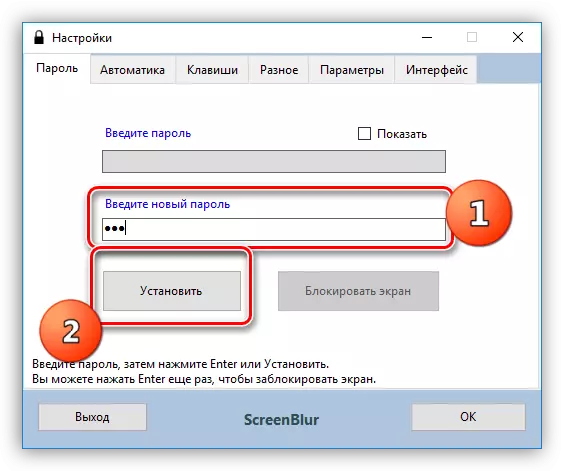
- In the main window, set a password to unlock. If this is the first launch, it is enough to enter the desired data in the field specified in the screenshot. Subsequently, it will be necessary to enter the old one to replace the password, and then specify a new one. After entering the data, click "Set".
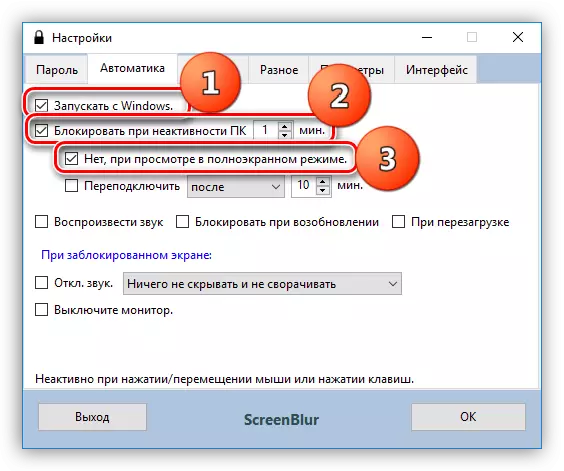
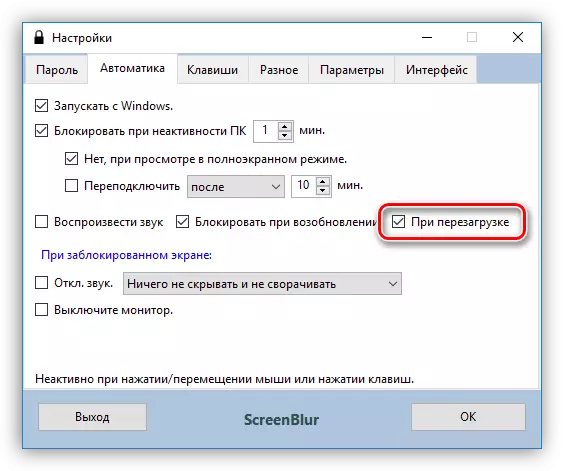
- On the Automatics tab, configure the work parameters.
- Turn on the startup when starting the system, which will allow you to not run ScreenBLUR manually (1).
- I exhibit the time of inactivity, after which access to the desktop will be closed (2).
- Disable the functions when viewing movies in full screen or games will help avoid false protection triggered (3).
- Another useful, in terms of security, the function is to lock the screen when the computer outputs from the sleeping or waiting mode.

- The next important setup is a ban on the reboot during the locked screen. This feature will start working only three days after installation or another password change.
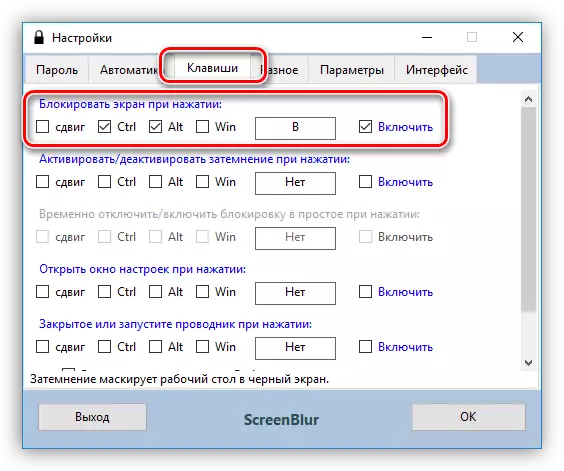
- Go to the "Keys" tab, which contains settings for calling functions using hot keys and, if required, set your combinations ("shift" is SHIFT - localization features).
- The next important parameter located on the "Miscellaneous" tab is a blocking action that continues a certain time. If the protection is activated, then the program will turn off the PC through the specified interval, translates it into sleep mode or leaves its screen.

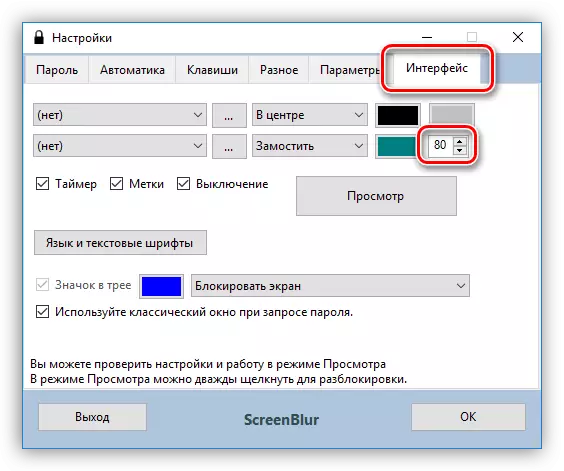
- On the Interface tab, you can change the wallpaper, add a warning to "intruders", as well as configure the desired colors, fonts and language. The opacity of the background image must be increased to 100%.
- To perform the screen lock, click the SCREENBLUR icon and select the desired item in the menu. If hot keys have been configured, you can use them.

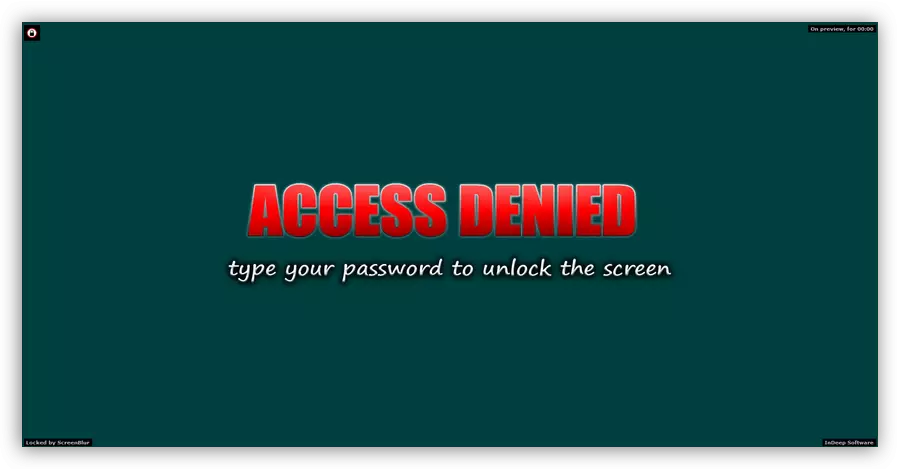
- To restore access to the computer, enter a password. Please note that no window will appear, so the data will have to enter blindly.
The second group can be attributed to a special software for blocking programs, such as Simple Run Blocker. With it, you can limit the launch of the files, as well as hide any media installed in the system or close access to them. It can be both external and internal disks, including systemic. In the context of today's article, we are only interested in this feature.
Download SIMPLE RUN BLOCKER
The program is also portable and can be run from any place on a PC or from removable media. When working with it you need to be more attentive, since there is no "fool protection". This is expressed in the possibility of blocking that disc on which this software is located, which will lead to additional difficulties when it starts and other consequences. How to fix the situation, let's talk later.
If an option was selected with a disk hide, then it will not be displayed in the "Computer" folder, but if you register the path in the address bar, then the "Explorer" will open it.
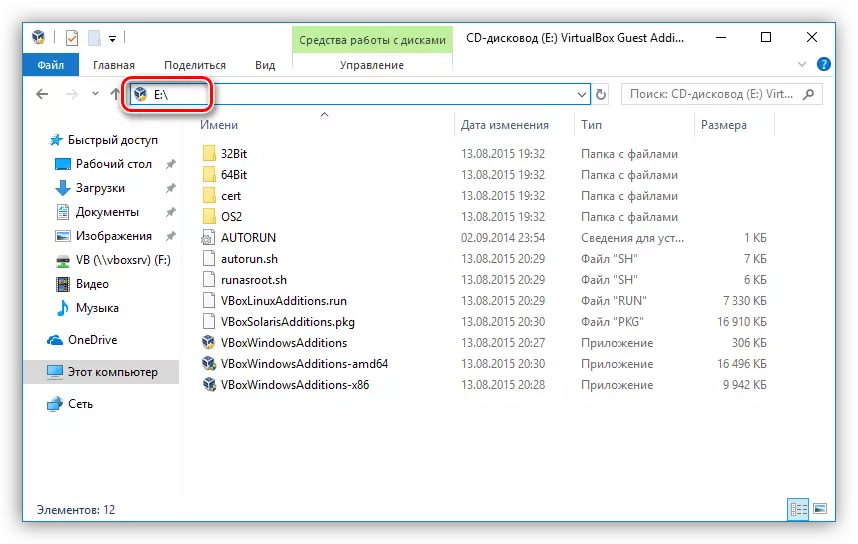
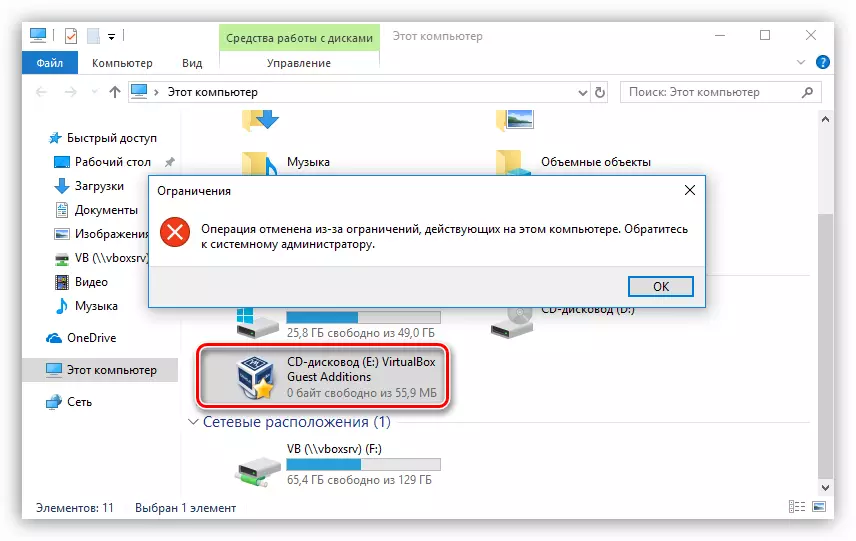
In the event that we chose the blocking, when you try to open the disc, we will see such a window:
In order to stop the execution of the function, you need to repeat the steps 1, then remove the checkbox opposite the media, apply the changes and restart the "conductor".
If you still closed access to the disk on which the folder with the program "lies", then the only output will be launched from the "Run" menu (Win + R). In the "Open" field, you must register the full path to the runblock.exe executable file and click OK. For example:
G: \ runblock_v1.4 \ runblock.exe
Where g: \ - the drive letter, in this case, the flash drive, runblock_v1.4 is a folder with a unpacked program.

It is worth noting that this feature can be used to even more improve security. True, if it is a USB disk or flash drive, then other removable media connected to a computer and which will be given this letter will also be blocked.
Method 2: Standard OS
In all versions of Windows, starting with the "seven", you can block the computer using the entire Kiji combination Ctrl + Alt + Delete, after pressing the window appears with a choice of action options. It is enough to click on the button "Block", and access to the desktop will be closed.
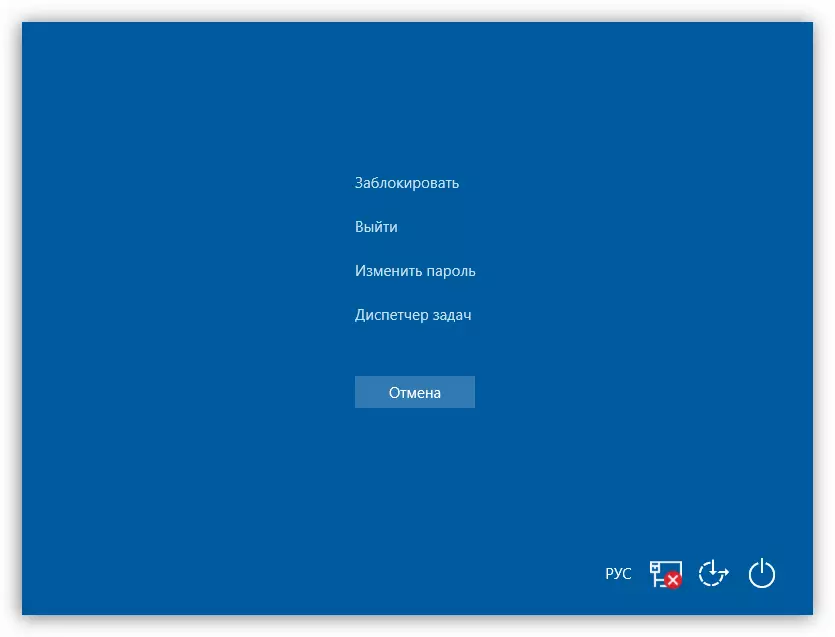
The fast version of the actions described above is universal for all Windows, a combination of Win + L, instantly blocking PCs.
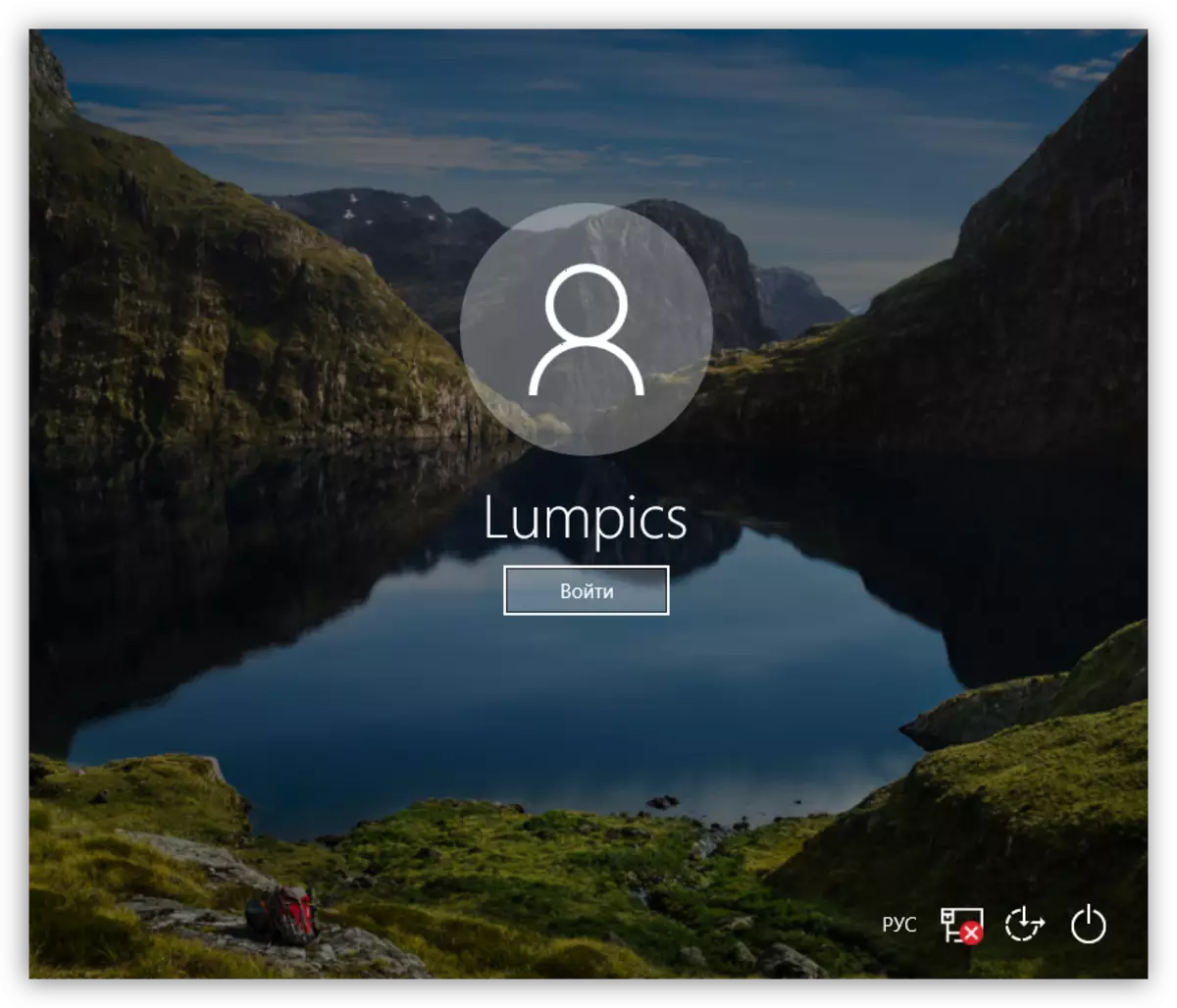
In order for this operation to have some sense, it has provided security, you need to install a password for your account, as well as, if necessary, for others. Next, we'll figure it out how to lock on different systems.
There is another way to install a password in the "dozen" - "Command Line".
Read more: Installing a password on Windows 10
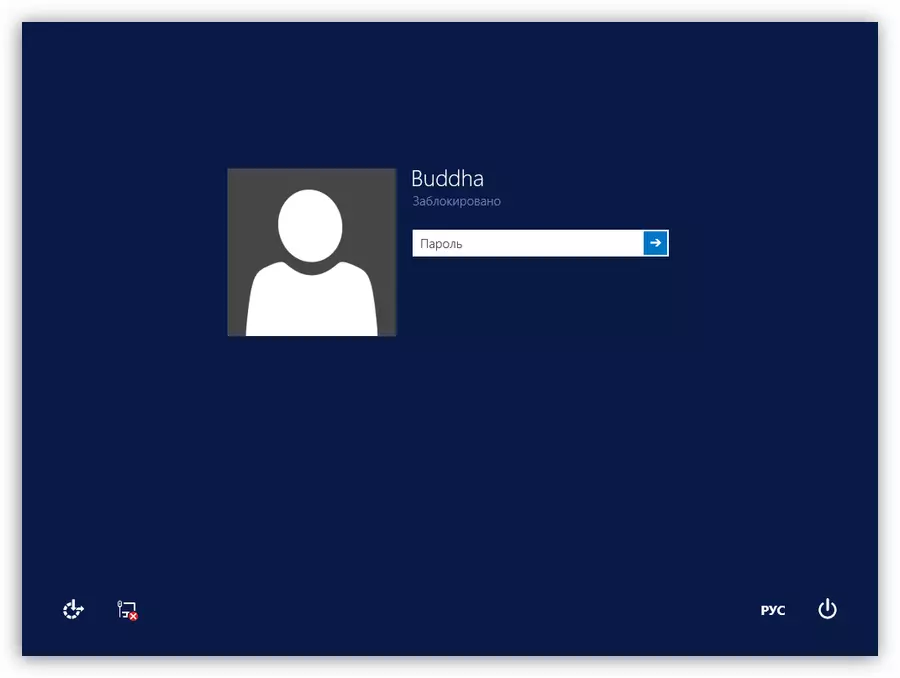
Now you can block the computer with the keys above - Ctrl + Alt + Delete or Win + L.
Windows 8.
In the "eight", everything is done a little easier - enough to get to the parameters of the computer on the application panel and go to the account settings, where the password is installed.
Read more: How to put a password in Windows 8

The computer is blocked by the same keys as in Windows 10.
Windows 7.
- The easiest option of the password setup in Win 7 is the choice of reference to your "account" in the "Start" menu, which has the view of the avatar.

- Next, you must click on the "Creating a password of your account".

- Now you can set a new password for your user, confirm and come up with a hint. After completion, you should save the changes to the "Create Password" button.
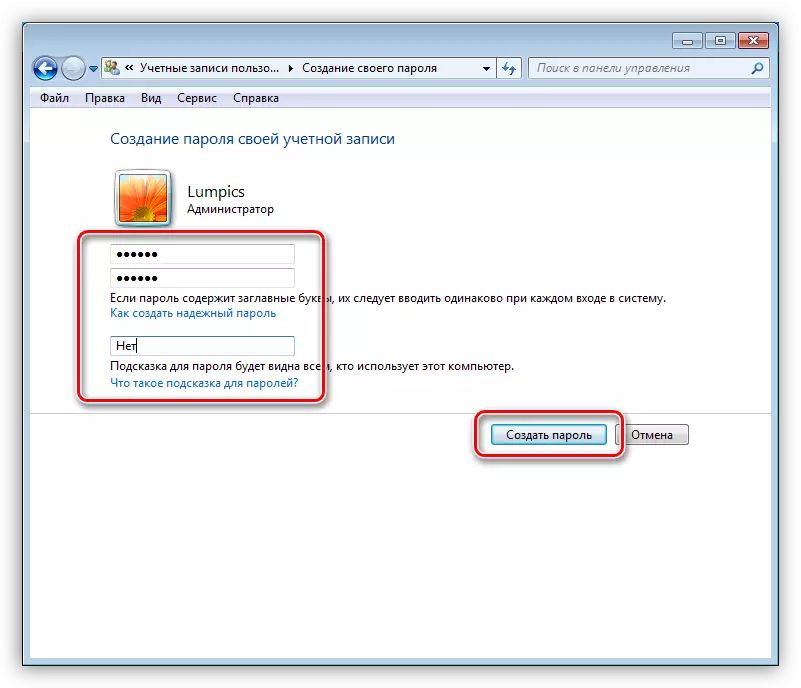
If there are other users on the computer besides other users, then their accounts should also be protected.
Read more: Installing a password on a Windows 7 computer
Locking the desktop is performed all the same key combinations as in Windows 8 and 10.

Windows XP.
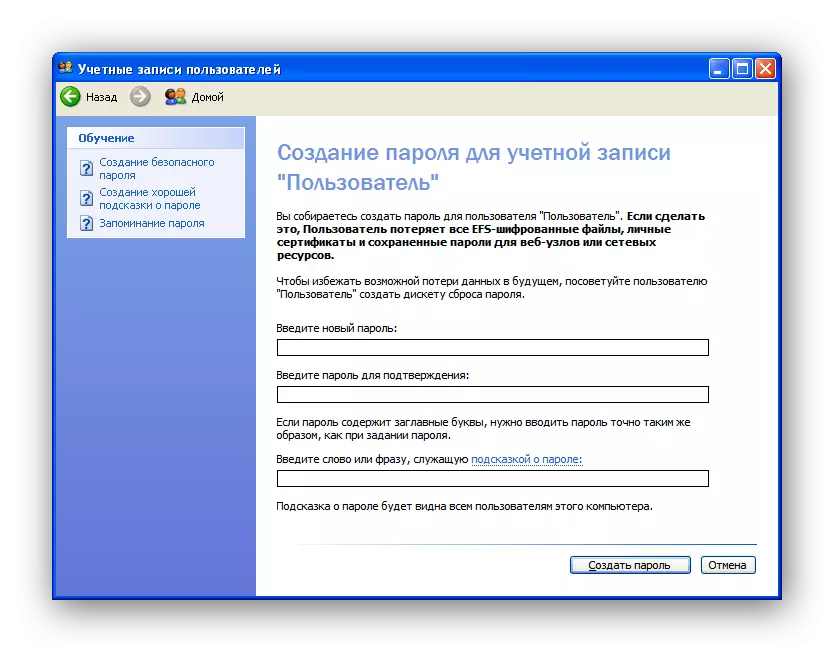
The procedure for installing a password in XP does not differ in particular complexity. Enough to go to the "Control Panel", to find the Account Settings section, where to perform the necessary actions.
Read more: Installing a password in Windows XP
In order to block the PC running this operating system, you can use the Win + L key combination. If you press Ctrl + Alt + Delete, the "Task Manager" window opens, in which you want to go to the "Shutdown" menu and select the appropriate item.

Conclusion
Blocking a computer or individual components of the system allows you to significantly improve the security of the data stored on it. The main rule when working with programs and system means is the creation of complex multivalued passwords and storing these combinations in a safe place, the best of which is the user's head.
